This article offers those who master the classic InTouch R14, a step-by-step instruction on setting up communication with devices using the Modbus TCP protocol. I’ll try to explain those features of the settings that can put a novice developer in a difficult situation.
1. Licensing
The company Klinkmann supports developers of their products, issuing full, but temporary licenses, each of which operates a little less than a month. After the expiration of this period both the development system and runtime stop working. It is required to repeatedly request and update license files.
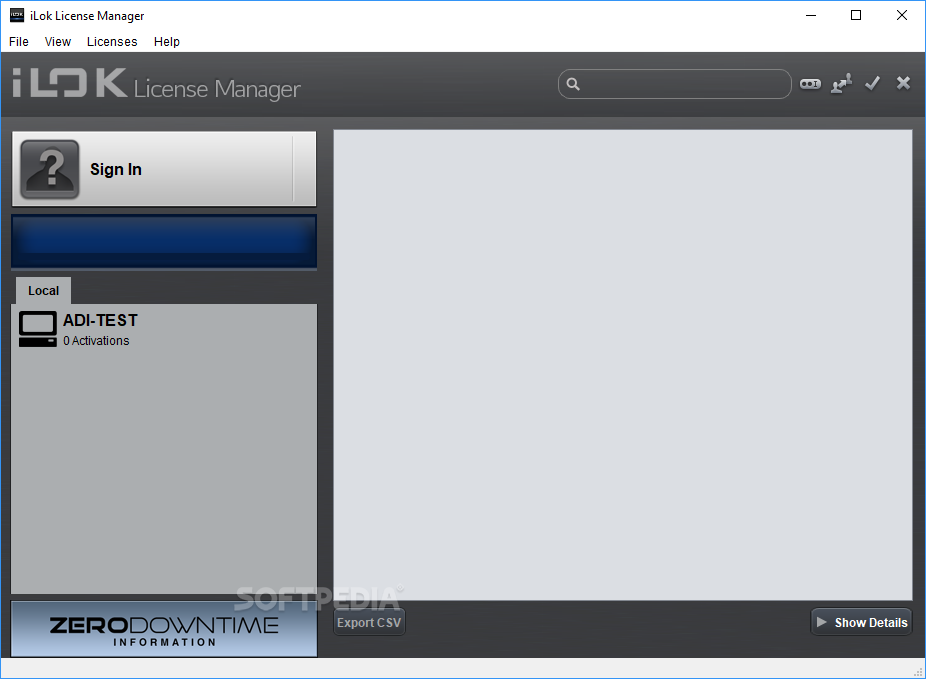
Usually three files are issued. All of these must be installed in the ArchestrA License Manager. It looks like this:
The absence of a license or an incorrectly installed license may be the cause of the lack of communication. After installing the license, it is desirable to reboot.
2. Download and install the integration package Server DA (DASMBTCP)
Detailed configuration instructions in the video:
Manage your risk capital as you build market share for your software products and cloud services, using our monthly subscription based software license management services. Our solutions mostly run in internal security zones so we have to support activation of licenses on systems that have no external network connections. Run the License Manager setup from your My Esri software download or from the ArcGIS installation media. Follow the instructions to install the license manager and FlexNet licensing service. At the end of the installation, ArcGIS License Server Administrator appears.
Wonderware License Manager
3. As an emulator of the MODBUS TCP operation, I usually use the product from Modbus Tools (Modbus Pool & Modbus Slave)
Immediately configure the data exchange to make sure that everything we have is working with the Modbus TCP protocol and data is being exchanged.
Attention!!!
ID is set to 255. Otherwise it will not work. Where to change this value in driver properties – yet did not find. If your Slave device has a different ID, then the working connection will not be achieved.
We disable the Modbus Pool, we do not need the port to be busy at the beginning of the connection.
4. Configure the Server DA driver (DASMBTCP)
Pay attention to the port number (for example, indicated 503)!
Here we form a common list of tags that will exchange data with the PLC
Help describes the signs that we can specify for correct data retrieval
5. Indication of parameters on video frame
We go in WindowMaker
Create an Access Name that will be associated with our topic and server
Next, create the required number of tags associated with the Access Name
Next on the video frame create a dynamic text
Linking (linking) it with the tag we need
6. Run the system Online (Runtime)
If there is no error anywhere, values similar to those in the Modbus Slave
I experimented a bit with disabling the drivers manually. I found out that when communication is lost, the values remain on the screen without changing, without giving out any indication of an error. This is certainly not suitable for the work of the industry. I will look for how to implement otherwise, for example, the replacement of values by the signs of the lattice. I will supplement this article later, when I find a solution
#InTouch, #stepbystep, #instructions, #settings, #drivers, #Modbus, #Stepbystepinstruction, #Stepbystep
1. EXECUTIVE SUMMARY
- ATTENTION: Exploitable remotely/Low skill level to exploit
- Vendor: AVEVA Software, LLC (AVEVA)
- Equipment: Wonderware License Server
- Vulnerability: Improper Restriction of Operations within the Bounds of a Memory Buffer
Wonderware Development License
2. RISK EVALUATION
Successful exploitation of this vulnerability may result in remote code execution with administrative privileges.
3. TECHNICAL DETAILS
3.1 AFFECTED PRODUCTS
The following versions of Wonderware License Server use the vulnerable Flexara Imgrd (Versions 11.13.1.1 and prior):
- Wonderware License Server v4.0.13100 and prior.
Only users with the Counted Licenses feature with “ArchestrAServer.lic” in Wonderware License Server are affected.
Wonderware License Server is delivered by:
- Wonderware Information Server 4.0 SP1 and prior, and
- Historian Client 2014 R4 SP2 P02 and prior.
3.2 VULNERABILITY OVERVIEW
3.2.1 IMPROPER RESTRICTION OF OPERATIONS WITHIN THE BOUNDS OF A MEMORY BUFFER CWE-119
Buffer overflows in lmgrd and vendor daemon in Flexera FlexNet Publisher may allow remote attackers to execute arbitrary code via a crafted packet, resulting in remote code execution with administrator privileges.
CVE-2015-8277 has been assigned to this vulnerability. A CVSS v3 base score of 9.8 has been calculated; the CVSS vector string is (AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H).
3.3 BACKGROUND
- CRITICAL INFRASTRUCTURE SECTORS: Chemical, Critical Manufacturing, Energy, Food and Agriculture, and Water and Wastewater
- COUNTRIES/AREAS DEPLOYED: Worldwide
- COMPANY HEADQUARTERS LOCATION: United Kingdom
3.4 RESEARCHER
An anonymous researcher reported this vulnerability to AVEVA, who then reported it to NCCIC.
4. MITIGATIONS
AVEVA recommends affected users install update “Hotfix Wonderware License Server VU-485744” or later, which can be downloaded from:
https://softwaresupportsp.schneider-electric.com/#/producthub/details?id=5076 (login required)
AVEVA has published Security Bulletin LFSEC00000129. It can be found at the following location:
NCCIC recommends users take defensive measures to minimize the risk of exploitation of this vulnerability. Specifically, users should:
- Minimize network exposure for all control system devices and/or systems, and ensure that they are not accessible from the Internet.
- Locate control system networks and remote devices behind firewalls, and isolate them from the business network.
- When remote access is required, use secure methods, such as Virtual Private Networks (VPNs), recognizing that VPNs may have vulnerabilities and should be updated to the most current version available. Also recognize that VPN is only as secure as the connected devices.
NCCIC reminds organizations to perform proper impact analysis and risk assessment prior to deploying defensive measures.
NCCIC also provides a section for control systems security recommended practices on the ICS-CERT web page. Several recommended practices are available for reading and download, including Improving Industrial Control Systems Cybersecurity with Defense-in-Depth Strategies.
Additional mitigation guidance and recommended practices are publicly available on the ICS-CERT website in the Technical Information Paper, ICS-TIP-12-146-01B--Targeted Cyber Intrusion Detection and Mitigation Strategies.
Organizations observing any suspected malicious activity should follow their established internal procedures and report their findings to NCCIC for tracking and correlation against other incidents.
No known public exploits specifically target this vulnerability.
Contact Information
For any questions related to this report, please contact the CISA at:
Email: CISAservicedesk@cisa.dhs.gov
Toll Free: 1-888-282-0870
For industrial control systems cybersecurity information: https://us-cert.cisa.gov/ics
or incident reporting: https://us-cert.cisa.gov/report
CISA continuously strives to improve its products and services. You can help by choosing one of the links below to provide feedback about this product.
This product is provided subject to this Notification and this Privacy & Use policy.
Please share your thoughts.
We recently updated our anonymous product survey; we'd welcome your feedback.

Comments are closed.